Understanding the Cynefin Framework - Navigating Complexity in Decision-Making
In today’s fast-paced and intricately connected world, decision-making has become an increasingly complex task. The Cynefin Framework, developed by Dave Snowden in 1999, offers a practical approach to understanding and addressing this complexity. This blog post delves into the fundamentals of the Cynefin Framework and explores how it can be effectively used in various organizational contexts.
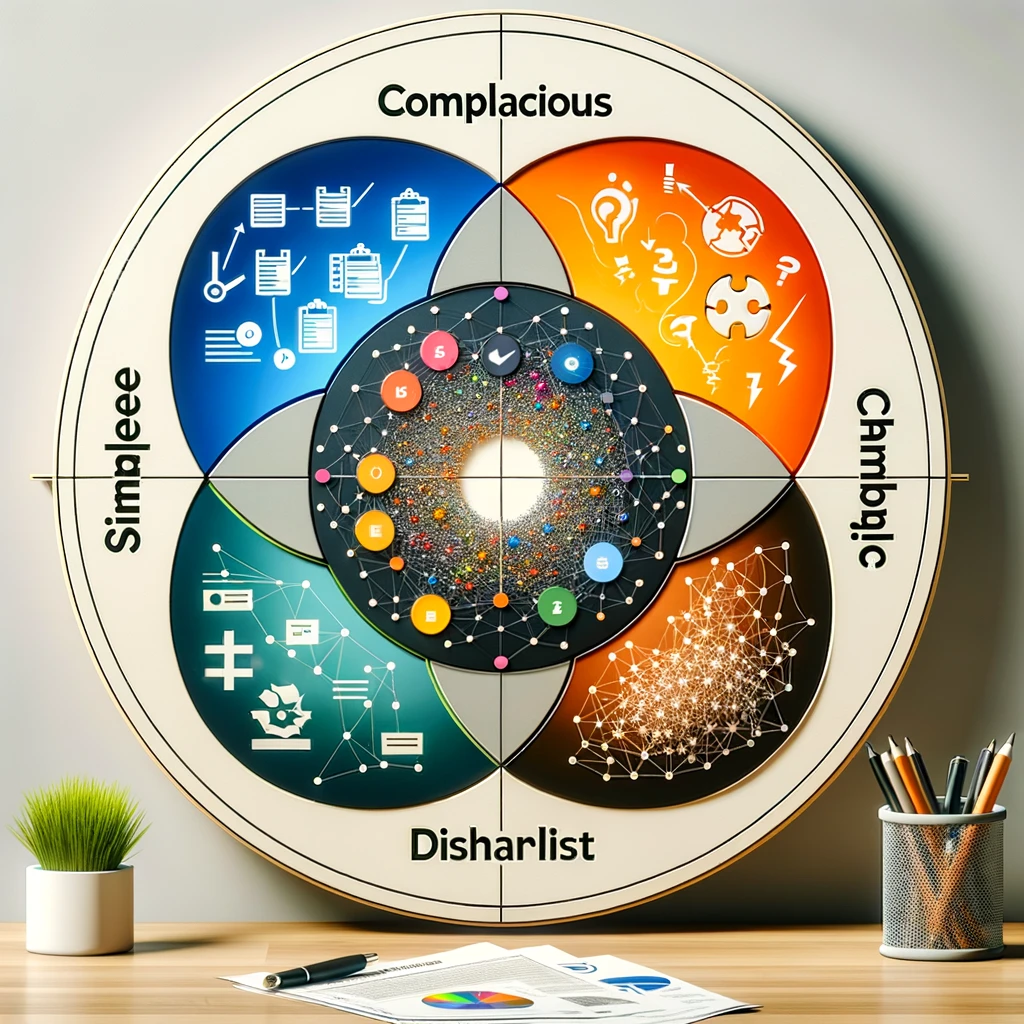
What is the Cynefin Framework?
The Cynefin Framework (pronounced "kuh-nev-in") is a conceptual tool designed to help leaders, managers, and decision-makers navigate the complexity of real-world situations. It offers a typology of contexts that guides users in identifying the nature of the challenges they face and selecting appropriate strategies for action.
The Five Domains of Cynefin
The framework categorizes problems and situations into five domains:
-
Simple/Obvious: These are situations where cause and effect are clear, and the right answer is evident. Best practice is applied here.
-
Complicated: In this domain, cause and effect are not immediately apparent but can be discerned through analysis or expertise. Good practice is often used in these scenarios.
-
Complex: Here, cause and effect are only visible in retrospect. These situations require probing, sensing, and responding. Emergent practice is necessary in this domain.
-
Chaotic: In chaotic contexts, there is no clear relationship between cause and effect. Rapid, decisive action is needed to establish order and prevent damage.
-
Disorder: This is the central domain, representing confusion or situations where it is unclear which of the other four domains applies. Identifying the correct domain is the first step in moving forward.
Applying the Cynefin Framework
1. Problem Identification:
- Simple/Obvious: Identify the problem, categorize it, and apply a known solution.
- Complicated: Engage experts to analyze and diagnose, then apply existing methodologies or create new ones.
- Complex: Experiment and learn by trial and error. Engage in a pattern of probing, sensing, and responding.
- Chaotic: Act immediately to re-establish order, then understand the situation and respond accordingly.
2. Leadership and Management Implications:
- In Simple contexts, traditional command-and-control approaches can work well.
- Complicated contexts benefit from a more analytical and expert-driven approach.
- Complex situations require a more adaptive leadership style, promoting innovation and creativity.
- In Chaotic scenarios, rapid decision-making and clear directives are crucial.
3. Organizational Learning and Adaptation:
- Organizations can use the Cynefin Framework to adapt their strategies, structures, and processes based on the nature of their challenges.
- It encourages a shift from a one-size-fits-all approach to a more nuanced understanding of different situations.
Conclusion
The Cynefin Framework is a powerful tool for understanding and responding to the complexities of modern decision-making. By categorizing problems into distinct domains, it helps leaders choose appropriate strategies and actions. In a world where one misstep can lead to significant consequences, having a structured approach to complexity is invaluable. Whether you are leading a small team or a large corporation, the Cynefin Framework can provide clarity and direction in a complex and uncertain world.
By embracing the principles of the Cynefin Framework, organizations can improve their decision-making processes, adapt to changing circumstances, and navigate the complexities of their environments more effectively.