Microsoft Fabric - Revolutionizing Data Analytics in the AI Era
Welcome back to Continuous Improvement. I'm Victor Leung, and in today's episode, we're diving deep into a solution that's reshaping the landscape of data analytics and AI integration—Microsoft Fabric. In a world where data is akin to the lifeblood of AI, managing and utilizing this data effectively is crucial for any organization's success. Microsoft Fabric offers a streamlined approach to this challenge, ensuring that data isn't just collected but is also effectively harnessed.
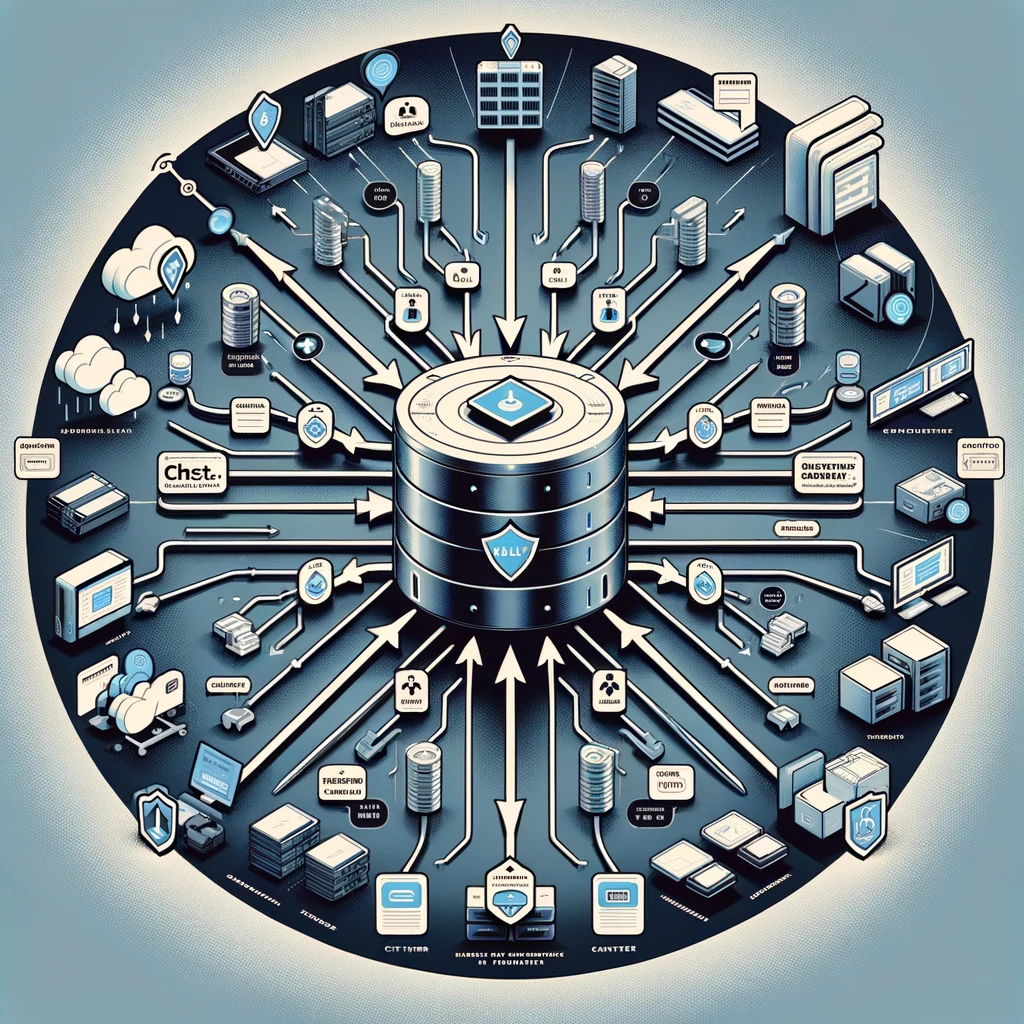
The rise of disparate tools for data handling—from Hadoop to Spark—has often left CIOs feeling more like Chief Integration Officers. Microsoft Fabric is designed to address this by unifying these diverse systems into a cohesive, integrated stack. Let’s explore how this platform is moving us from fragmentation to unity in the realm of data analytics.
Microsoft Fabric is built on four core design principles that make it a game-changer for businesses. First, it’s a Complete Analytics Platform—unified, SaaS-fied, secured, and governed. This means all your data analytics needs are met under one roof without the hassle of juggling multiple tools.
Secondly, the platform is Lake Centric and Open. At its heart lies the principle of "One Lake, One Copy," which emphasizes maintaining a single data lake that is open at every tier. This not only ensures flexibility but also enhances the openness of your data systems.
Thirdly, Microsoft Fabric aims to Empower Every Business User. With seamless integration into Microsoft 365, the platform is designed to be intuitive and familiar, enabling users to effortlessly turn insights into action.
And lastly, AI Powered. Fabric isn’t just using AI; it embeds generative AI into the platform, enhancing every aspect of data interaction, from analytics to management, ensuring that your decisions are informed by the most intelligent insights available today.
Transitioning from legacy systems like Azure Data Factory to this SaaS-fied experience means that businesses can now enjoy a more streamlined, cost-effective, and scalable approach to data management. Microsoft Fabric essentially acts as the OneDrive for data through its OneLake feature, providing a single, organized, and indexed SaaS lake that simplifies data discovery, governance, and compliance.
Another standout feature of Microsoft Fabric is Copilot, an AI assistant that helps users enrich and analyze data within notebooks. Imagine being able to converse with your data, asking questions, and modeling predictions through a simple dialogue. Copilot makes this possible, enhancing productivity and understanding across your team.
In conclusion, Microsoft Fabric represents not just a technological evolution but a strategic revolution in how we handle data in the digital age. By adhering to its core principles, it promises a unified, flexible, and profoundly intelligent approach to data analytics.
Thank you for joining me on Continuous Improvement as we explored the transformative capabilities of Microsoft Fabric. For more insights into how technology can revolutionize your business processes, make sure to subscribe to our podcast. Until next time, keep pushing the boundaries of what's possible and continue to improve.